Librebooting The Gigabyte GA-G41M-ES2L
Chances are the computer you are using right now has a vulnerable backdoor on it right now. Introduced in June of 2006, Intel's Intel Management Engine (ME) is a separate computing environment that is physically located in the Graphics and Memory Controller Hub chip located on the motherboard. The Intel ME is present on all desktop, mobile (laptop), and server systems since mid 2006. Without going too much into detail here, the Intel ME runs its own tiny OS and has unrestricted access to all components on the motherboard including CPU, all RAM addresses, Networking, and hard drive(s).
The Intel Management Engine with its proprietary firmware has complete access to and control over the PC: it can power on or shut down the PC, read all open files, examine all running applications, track all keys pressed and mouse movements, and even capture or display images on the screen. It has a network interface that is demonstrably insecure, which can allow an attacker on the network to inject rootkits that completely compromise the PC and can report to the attacker all activities performed on the PC. It is a threat to freedom, security, and privacy that can’t be ignored.
How do I get rid of this?
There are some requirements that you need to have before you start. One of those is that you must have a system that has Intel ME that is under version 6.0 (systems from 2008/2009 and earlier). This is because this was before Intel started to sign the ME software with a signature key. You cannot replace the boot firmware and get rid of Intel ME on systems newer than this because of this reason.
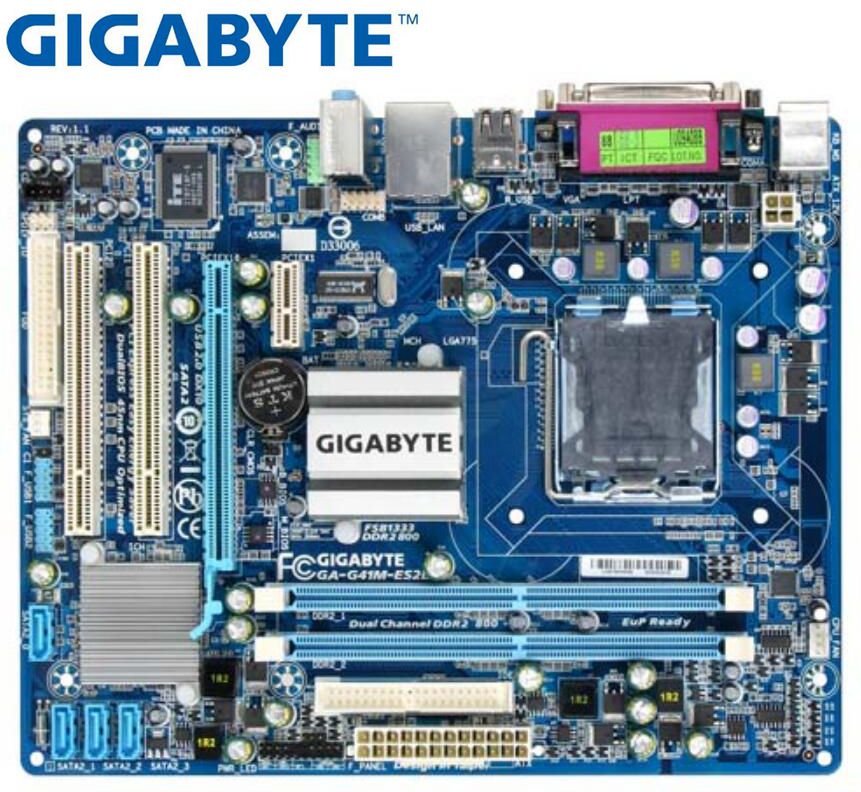
The system that I used was a Gigabyte GA-G41M-ES2L motherboard.
Libreboot
I replaced the BIOS software on this board with something called Libreboot. Libreboot is a fork of Coreboot, which is an opensource boot firmware alternative for several supported pieces of hardware. Libreboot differs from coreboot in that Libreboot does not use any proprietary binary blobs at all so it is 100% open source and you can check it out for yourself on their Github.
In order to download libreboot you can go here and go to an HTTPS mirror of your choice. From there go into the /stable branch and download the latest release.
Flashing Libreboot
Getting the new boot firmware on the motherboard is actually not a complicated process with this specific motherboard since we can do it all from software. The first thing you are going to have to do is boot into a GNU+Linux distribution such as Debian. Once you are booted in you need to make sure you have a piece of software called flashrom. flashrom is a utility for identifying, reading, writing, verifying and erasing flash chips. It is designed to flash BIOS/EFI/coreboot/firmware/optionROM images on mainboards, network/graphics/storage controller cards, and various other programmer devices.
Use your package manager software to get flashrom:
# sudo apt install flashrom
We then want to issue the following commands to flash the compiled libreboot binary file to the actual chips. The reason we are flashing twice is because this particular motherboard has 2 flash chips on it - one is the main one and the other is a backup for the main chip just in case something happens to it.
Flash the first chip:
# ./flashrom -p internal:dualbiosindex=0 -w libreboot.rom
Flash the second chip:
# ./flashrom -p internal:dualbiosindex=1 -w libreboot.rom
If the flashes were successful you should see something like this written at the end of the flashrom output:
verifying flash... VERIFIED.
Reboot
Thats pretty much it for the flashing, now we just need to reboot. When the CPU pulls the code from the flash chips on startup it will be executing opensource and free boot firmware instead of the proprietary spyware junk that I talked about above. When we flashed the libreboot rom to the chips, it pretty much fully disabled the Intel ME.